The Undercover MacBook
For someone in possession of a stolen computer it is no longer enough to look over their shoulder while using it, these days the computer itself can turn informer and lead the police straight to them.
This summer I had my MacBook Air stolen from a hotel room while vacationing in Las Vegas. Along with the machine, roughly 1500 photos taken during the preceding three week road-trip through California and Nevada were gone. Thanks to my heavy reliance on the cloud storage service Dropbox I lost almost no other data, despite having used this as my main machine for the last couple of months. I would have been devastated had I for example lost the source codes to my apps.
I promptly made a report of the theft to the Las Vegas Metro Police Department where they let me know, in no uncertain terms, that I should not expect to see my computer again. They did however assign a detective, one Russel Lee to the case.
A Ray of Hope
Despite the Police's pessimism, I maintained a ray of hope. After buying the laptop I had invested in a piece of software called Undercover to keep my MacBook safe. Described as a “revolutionary theft-recovery software” it would supposedly provide me with all the information needed to recover the computer in case it was ever stolen.
Using my iPad I logged on to the Undercover recovery center website and marked my computer as missing — telling the software to start tracking it.
Things were quiet for several days. I had already made my way back to Sweden and the ray of hope was starting to fade when I finally received an e-mail proclaiming that the computer had been used to access the internet and that Undercover had started tracking it. As promised, I was provided with webcam photos, screenshots, the computer’s IP address, and an approximate location!
I could see that the person using it had logged in to the computer’s guest account and had connected to a Wifi network. While it’s no fun seeing someone using your computer without your consent, I was nevertheless relieved that the tracking software seemed to be working.

Hello there, what are you doing with my laptop?

Oh, you’re hitting up women on Facebook. Carry on then.
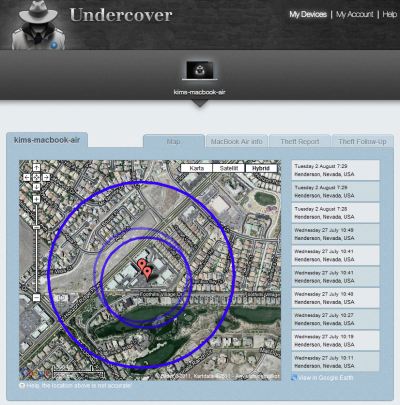
The location in Henderson, Nevada, wasn’t exact enough for the police to figure out which house to visit. Frustratingly, I also found out that it takes the police all of 60 days to get the subscriber information for an IP address.
Profiling the User
During the following weeks I was informed whenever the computer was used and I tried to piece together the information I could gather from the screenshots in an effort to point the police in the right direction. I quickly found out the user’s Facebook profile and Skype account, but he used the alias Dee Macc and I couldn’t figure out his real name and address. His Facebook profile did mention that he graduated from LA High class of 2007, so that prompted a search of their online yearbook, alas to no avail.

Eventually a bit of luck, he typed his phone number into a couple of chat windows while trying to pick up women. But according to whitepages.org the number he gave is registered to a 60 year old person in Los Angeles. Not the age you would expect of someone who uses the phrase “im not no baby yeah”. Also, according to his Facebook profile Dee Macc was born on February 5th 1990 making him 21 years old. Thus, the registered owner of the phone number is definitely not our man.


It looked as if my machine was making lots of new friends as other people also started using it now and then, always from the same location in Henderson, NV. Some of their Facebook profiles were under their real names. One of those people, let’s call him B., turned out to be the owner of a Las Vegas boxing gym near Las Vegas Boulevard. Another user was his son D., whom I could tell from his Facebook account is a promising young boxer.
As time passed and more information came in I forwarded everything to the police, but they still didn’t have enough to take action.
The Retrieval
One late evening as I was ready to turn in for the night I was alerted by Undercover that the computer had moved to a new location. At first I thought this was bad news since it meant the IP address subpoena would have to be restarted from scratch, but I couldn't have been more wrong. The location was reported to be close to Las Vegas Boulevard, and the webcam photos showed D. hanging out in a very nice boxing gym. For the first time in weeks I knew exactly where it was!
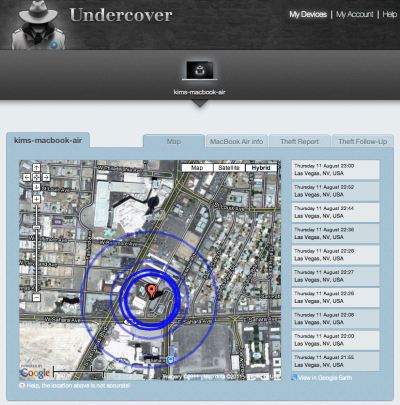


I sent a quick e-mail to Detective Lee.
New and actionable information.
D. XXXXX is at the time of me writing this using the computer at the XXX XXXXXX Boxing Gym, XXXX Paradise Road, Las Vegas.
I had a reply just minutes later
Perfect! Thanks, I’ll run over there and see.
As webcam photos continued to come in over the next few minutes, I forwarded them to Detective Lee to help him find the right people in the gym. Then all of a sudden the computer went offline. A worrying turn, but I maintained hope as the last screenshot contained an intriguing Facebook update.

“ugghhh i hate police officers…makes me wanna qweef”
Moments later the e-mail I had been hoping for arrived from Detective Lee.
I have your computer! Good Job!!
High fives all around! The Undercover software had delivered on its promise, and combined with the swift action from Detective Lee it had recovered my MacBook Air.
Conclusion
As I’m writing this I have just taken delivery of the computer from the Las Vegas Metro Police Department evidence vault, and I was glad to see my road-trip photos remain safely stored on the disk. Detective Lee had already mentioned that my user account was still on the computer which lead me to believe they would be there, but it’s good to have it confirmed.
After 10 weeks of being separated from my computer I can finally get back to app development and get som delayed updates out the door — once I'm done organizing the road-trip photos of course.
Lessons learned
I was lucky in having been sufficiently prepared before having my computer stolen. Take these lessons to heart, should it happen to you;
- It’s a good idea to take the precaution of having theft-recovery software installed on your computer.
- It is vital to have your computer’s serial number available when filing the police report, without it you may not be able to legally prove it’s yours even if you are able to track it.
- Set up a guest account so the thief can log in and connect to a network, or tracking will not work.
- Lock your user account whenever you step away from the computer so that a thief can’t access your files and won’t have administration privileges to the system.
This ordeal has made me consider taking a couple of additional measures now the computer is back in my possession.
- For insurance reasons always make use of the hotel in-room safety box, no matter how insecure.
- Set a firmware password, a simple measure which will make it impossible for a thief to wipe the system and reinstall the operating system, thus removing the tracking software.
- Install some software to allow me to siphon off data in the background so that I could have copied over my photos while the computer was connected to the internet but not under my control.
Undercover is available from Orbicule. I highly recommend you install it on your Macs.
Excerpts of collected evidence
Below are some of my favorite screenshots and webcam photos selected from the huge amount of data I received from Undercover during this episode.

Installing Flash? Not on my computer you don’t!





Some webcam photos of people hanging out with my MacBook Air.
“yu cute” — Dee Macc using the shotgun approach on Taberah and Gisele.

“im not no baby yeah” — Dee Macc's failed attempt at sounding mature.
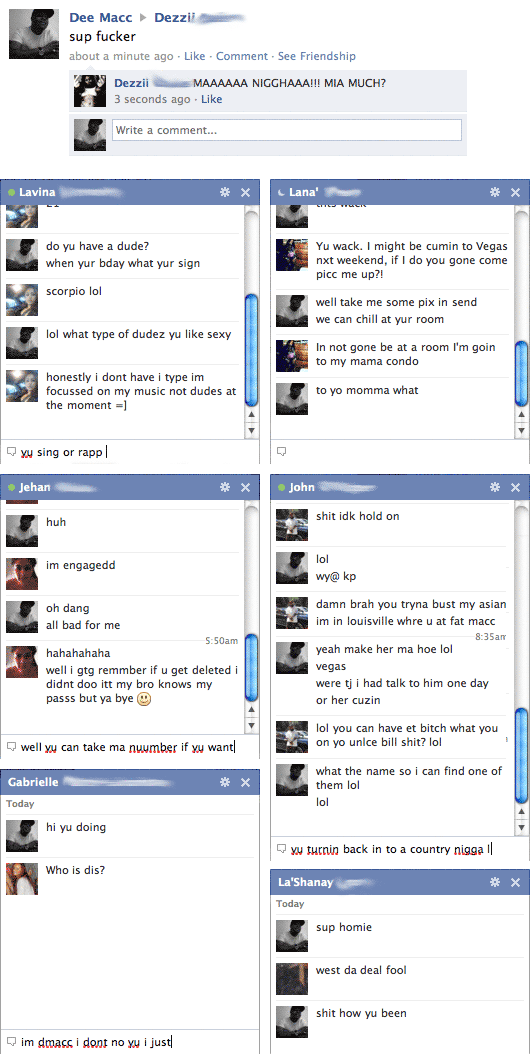
Fine prose from Dee Macc and friends.